ZeroAccess behavior has changed lately. Now it installs an extra service. This service seems to act as a protection mechanism for the rootkit to help it survive reboots. TDSSKiller seems to do a good job of finding both the infection and the service. Some of you may have seen the service some up as Backdoor.Multi.ZAccess.gen in TDSSKiller. TDSSKiller shouold not be used on ZeroAccess as anything more than a detection tool if you want to be 100% safe.
Tools you will need:
o XueTr by linxer - http://www.xuetr.com/download/XueTr.zip
o Avenger by SwanDog64 - http://swandog46.geekstogo.com/avenger2/avenger2.html
First, you will need to run XueTr. Once you open it up, you may or may not see a message like this:
The first thing we want to look for is the Object Hijack in the Kernel tab. This tab will help us verify that the infection is active and which system file is being affected. With an active infection, you should have 4 objects in the Object Hijack tab: 2 hijacks on the MBR, 1 Abnormal Driver, and 1 Hijacked Kernel Module. By looking at the Kernel Module that has been hijacked, we can determine which file needs to be replaced.
Everything needs to be done in a specific order or this will not work properly. Additionally, we want to make sure all other programs are closed and that any AV software is deactivated before moving forward. We also need to make 100% sure that system restore is enabled and in a working state, and that we create a restore point prior to moving any further into the disinfection process.
Our next step is to find a good copy of the driver, I will leave that part to you. Once you have your clean driver, place it onto the C:\ drive of the infected PC. We will now need to open up our Avenger tool and write a script for it. The script for ZeroAccess is fairly straight-forward but if you would like to read more about Avenger and how the scripting is done, you can find the information on the SwanDog64 website noted above. Assuming that the infected driver is ipsec.sys, the script should read as follows:
Files to Move:
C:\ipsec.sys | C:\Windows\System32\Drivers\ipsec.sys
We want to run the script. Select Yes.
We want to make sure that we do not reboot when asked by Avenger. We will reboot later once we have the rest of the infection taken care of. Select No.
Leave Avenger open and just minimize it. Next, we go back to XueTr and remove our MBR Hijack. Select the Ring0 Hooks tab, then the Disk tab. You will see a message saying "Existed DR0 AttachToDevice Hijack, Do you restore it..." Yes you do :)
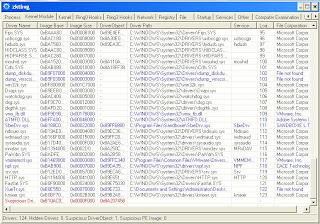
We have so far addressed the hijack on the kernel module(our Avenger script), and we have removed the MBR hijack, so we have 2 more steps to go. Next, we will deal with the service. You may find that some samples do not have the service, please skip this step if you do not have the service installed. You can find this by running TDSSKiller (it shows up as
Backdoor.Multi.ZAccess.gen ) Go to the Services tab. This one can be a bit tricky because it is named differently each time. The main things to look for here is that it is always abnormal, so XueTr will show up with blue highlighting on those services, it is always started by svchost.exe, File Corporation is Iomega or Oak Technologies, and it either has random letters and words for the description, or has the description:
"New service would allow parents to control their children's online activity".
There may be more than one of these services so you need to look carefully through this tab. Once you have found the service(s), right click and select delete. Please do not stop the service first, deleting it is enough and stopping usually has adverse effects.
We are now onto the last part, the Driver. Navigate to the Kernel Module tab. Scroll all the way to the bottom and you can see a Suspicious DriverObject that is highlighted in red. Right-click and select Delete Driver (File and Reg). Then we want to unload the driver. As XueTr tells us, this is dangerous and should always be the last step before reboot. Try to be quick when you reboot after unloading or you have the possibility of getting BSOD. Please keep that in mind and be cautious when performing this last step.
Yes you are sure you want to continue.
Once the driver has been unloaded, quickly move to the Setting tab and select Force System Reboot. Click Yes on the confirmation and wait for the system to reboot.
On successful reboot, you should see the Avenger results on the screen. If all went well, it will say that your file was successfully replaced. Now time to double check with XueTr, TDSSKiller is also fine to double check. Open it back up and navigate to the Kernel tab, then Object Hijack.
If there are 0 objects, then PC is clean.












No comments:
Post a Comment